CI/CD CLI v1.2
Integrating the Panoptica CI/CD CLI tool into the development workflow enables you to scan container images for potential security vulnerabilities. Panoptica CI/CD CLI tool can detect and block security issues pre-production, before they are merged into the main codebase and deployed to production environment.
Version 1.2 of Panoptica's CI/CD CLI supports displaying CLI results in the console UI.
In order to view scan results in the Panoptica console UI, you need an API Key. See CI/CD CLI Tool (Preview) for instructions on generating a Panoptica API Key and promoting its role to an Ops user.
Installation
In order to integrate Panoptica into your development workflow, you need to download the Panoptica CI/CD CLI tool.
To download the Panoptica CI/CD CLI tool, and configure permissions, select the tab that matches your OS and platform architecture, and run the relevant command:
curl -O https://download.panoptica.app/panoptica-cicd/1.2.0/artifacts/darwin-amd64/panoptica-cicd && chmod +x ./panoptica-cicd
curl -O https://download.panoptica.app/panoptica-cicd/1.2.0/artifacts/darwin-arm64/panoptica-cicd && chmod +x ./panoptica-cicd
curl -O https://download.panoptica.app/panoptica-cicd/1.2.0/artifacts/linux-amd64/panoptica-cicd && chmod +x ./panoptica-cicd
curl -O https://download.panoptica.app/panoptica-cicd/1.2.0/artifacts/linux-arm64/panoptica-cicd && chmod +x ./panoptica-cicd
curl -O https://download.panoptica.app/panoptica-cicd/1.2.0/artifacts/windows-amd64/panoptica-cicd && chmod +x ./panoptica-cicd
Usage
Help command
Combine the --help flag with any command to see usage instructions and available flags.
./panoptica-cicd --help
CLI Version
Use the version command to view the version of the CLI tool you have installed.
./panoptica-cicd version
Image Scanning
Integrate the Panoptica CI/CD CLI tool into your CI/CD pipeline – after the image build phase but before it is pushed to a registry – to block vulnerable images from ever reaching production.
Run the panoptica-cicd command to scan container images for vulnerabilities.
./panoptica-cicd [global flags] image IMAGE_NAME:TAG [--local] [--exit-on-severity <level>]
Flags
| Flag | Arguments | Description | Default |
|---|---|---|---|
--local | None | Whether to pull the image from a local Docker daemon | False. Pulls the image from the Dockerhub registry |
--exit-on-severity | Critical / High / Medium / Low / Information | If a vulnerability severity is found at or above the given severity, the scan will exit with code 1 | None. The scan will not exit when a severity of any level is found. |
Global Flags
For each supported scan, the following arguments can be set and used:
| Flag | Arguments | Description | Default |
|---|---|---|---|
--report | none | Whether to send a scan report to the Panoptica console UI. | False - Does not send a scan report to Panoptica platform. |
--report-endpoint | Specifies an API endpoint to send the scan reports to. Can be used to send scan reports to the EU backend. | https://api.us1.console.panoptica.app/api/scs/scan-reports/v1/scan-reports Can be set using the PANOPTICA_REPORT_ENDPOINT environment variable. | |
--api-key | The API Key to be used in order to send scan reports to Panoptica platform. | None. Can be set using the PANOPTICA_API_KEY environment variable. |
Argument overrides environment variables
Providing a command line argument for
--report endpointor--api-keywill override any settings defined as environment variables.
Results
You can view the results of the image scan in the CLI, or in the Panoptica console UI.
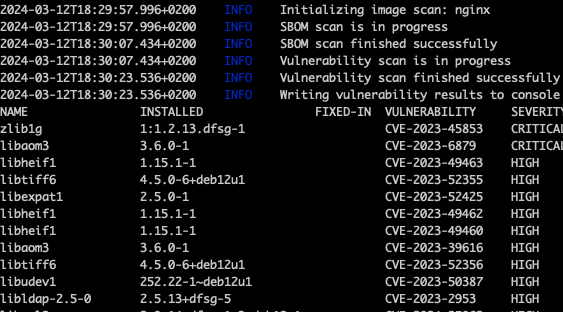
CLI output
This sample of output from the Panoptica CI/CD CLI tool displays a list of vulnerabilities found with specific details about package name, version, fixed version, CVE, and severity.
CI/CD Scan Results
If the --report flag is set to true, you will be able to view scan reports in the Panoptica console UI, on the CI/CD Scans tab under Build and Applications . Note that you'll need to [generate an API Key](doc:cicd-cli-tool# generate-api-key) and include it with the --api-key flag.
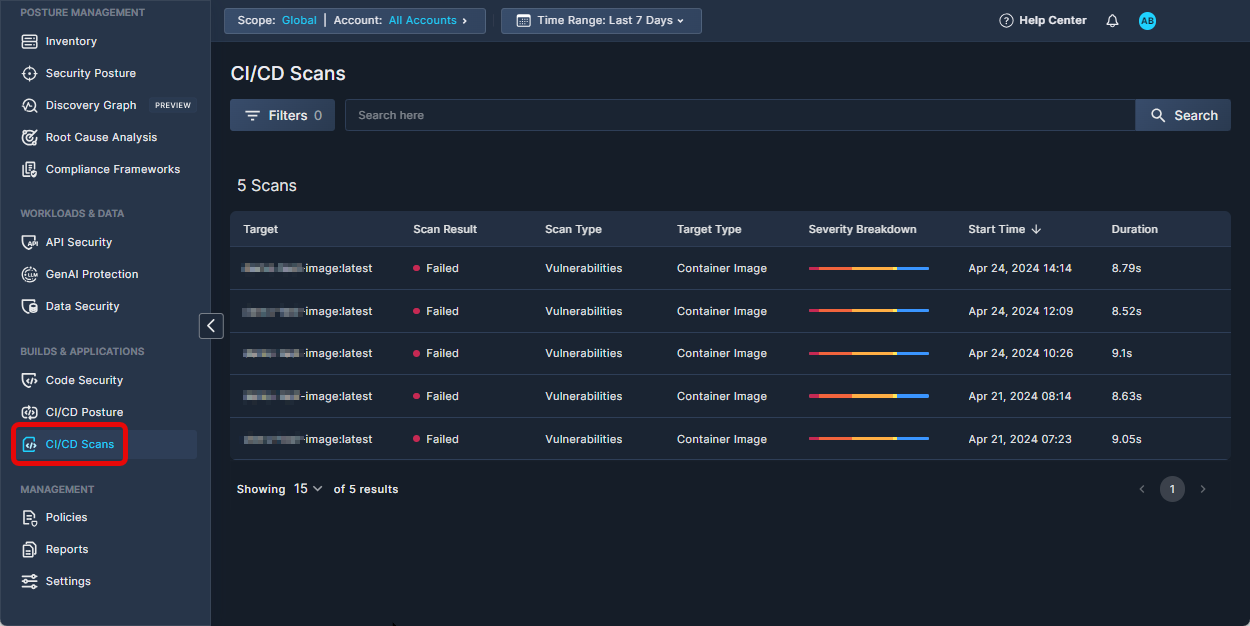
Click any scan record in the table to view a detailed report of the scan results.
Integration example: GitHub Actions
The Panoptica CI/CD CLI tool can be employed with any build system. Integration is straightforward, and is no different from running the tool locally.
Sample workflow:
name: Image Scan
on:
pull_request:
branches:
- main
jobs:
panoptica-cicd-scan:
runs-on: ubuntu-latest
steps:
- name: Checkout
uses: actions/checkout@v4
- name: Set up Docker Buildx
uses: docker/setup-buildx-action@v3
- name: Build Docker image
uses: docker/build-push-action@v5
with:
context: .
load: true
tags: my-image:latest
- name: Install Panoptica CICD CLI
run: |
curl -O https://download.panoptica.app/panoptica-cicd/1.2.0/artifacts/linux-amd64/panoptica-cicd && chmod +x ./panoptica-cicd
- name: Run image scan
run: |
./panoptica-cicd image my-image:latest --local --exit-on-severity high
Local image scanning
For local image scanning, the Docker daemon must be running, and have access to the scanned image.
Updated 7 months ago
