Azure CVE Scanning
Overview
Panoptica supports scanning for CVEs and malware in your Azure environment, without installing any agents on the instance. The scanning takes place using an orchestration layer that takes snapshots of the instances and scans them offline, without impacting your environment.
In order to facilitate the creation of the agentless CVE scan infrastructure, you create a custom role called panoptica-CVE-scanning during onboarding. This role defines the permissions required to managing the scanning resources, including creating and managing compute instances for the scans, as well as network resources for management and communication with the Panoptica platform.
Learn more about CVEs in Panoptica at Vulnerability Management.
Prerequisites and Limitations
- Microsoft Entra ID (formerly Azure AD) Premium P1 or Premium P2 is required to create the custom role. More information can be found here: Available versions of Microsoft Entra multifactor authentication
- The subscription type must be one of the following: Enterprise Agreement, Pay-As-You-Go (Offer code 003O), Sponsored (Offer code 0036P or 0136P), or Cloud Service Provider (CSP).
- Scan speed and availability depends on the available quota.
- For the available quota, the orchestrator layer launches up to 10 VMs over VMSS.
- CVE and malware scanning must have at least the following available quota:
- VM total cores per subscription, per region: 40 (Default: 20)
- Azure Spot VM total cores per subscription, per region: 40 (Default: 20)
- VM per series, such as A, Av2, Dv2, and F, cores per subscription, per region: 40 (Default: 20)
See Virtual Machines limits in Azure's documentation for more information.
To learn how to request additional quotas, see Azure's documentation.
Onboarding
The CVE and malware scanning is performed by a VM with an external volume attached to it. The base VM image is Panoptica's image. For the image to be more widely available, we copy the VHD to your storage account. It is then converted to a disk image and to an image version in a gallery in the 'East US' region (or UK South for customers based in the EU). The image will then be available to other locations as well.
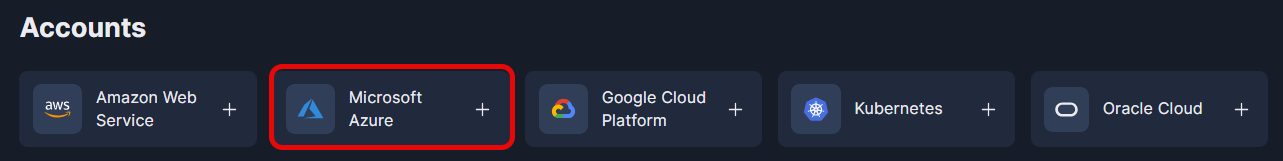
To get started, select Settings in the navigation pane, then the Accounts tab.
Choose Microsoft Azure, and follow the on-screen instructions, which are detailed at Azure Onboarding.
If you prefer to onboard your account manually, please visit Azure Onboarding - Manual Deployment.
In both methods, make sure to select Enable CVE & Malware scan on the Azure onboarding screen.
Supported Locations
CVE and malware scanning is available in the following Azure locations:
| Location | Location code |
|---|---|
| (Asia Pacific) Australia East | australiaeast |
| (Asia Pacific) Australia Southeast | australiasoutheast |
| (South America) Brazil Southeast | brazilsouth |
| (Canada) Canada Central | canadacentral |
| (Canada) Canada East | canadaeast |
| (Asia Pacific) Central India | centralindia |
| (US) Central US | centralus |
| (Asia Pacific) East Asia | eastasia |
| (US) East US | eastus |
| (US) East US 2 | eastus2 |
| (Asia Pacific) Japan East | japaneast |
| (Asia Pacific) Japan West | japanwest |
| (Asia Pacific) Korea Central | koreacentral |
| (Asia Pacific) Korea South | koreasouth |
| (US) North Central US | northcentralus |
| (Europe) North Europe | northeurope |
| (US) South Central US | southcentralus |
| (Asia Pacific) Southeast Asia | southeastasia |
| (Asia Pacific) South India | southindia |
| (Europe) UK South | uksouth |
| (Europe) UK West | ukwest |
| (US) West Central US | westcentralus |
| (Europe) West Europe | westeurope |
| (Asia Pacific) West India | westindia |
| (US) West US | westus |
| (US) West US 2 | westus2 |
Supported OS Versions
| OS | Version |
|---|---|
| Alpine | 3.3 and later |
| Ubuntu | 14, 16, 18, 20, 21, 22 |
| Debian | 8, 9, 10, 11 |
| RHEL | 5, 6, 7, 8, 9 |
| Fedora | 32, 33, 34, 35 |
| Oracle Linux | 5, 6, 7 |
| CentOS | 6, 7, 8, stream8, stream9 |
| AlmaLinux | 8, 9 |
| Rocky Linux | 8 |
| Amazon Linux | All |
| FreeBSD | 10, 11 |
| openSUSE | tumbleweed |
| openSUSE Leap | 11, 12, 15 |
| SUSE Enterprise | 11, 12, 15 |
| Raspbian | Jessie, Stretch, Buster |
Required Permissions
The custom role that you create when enabling CVE scanning (panoptica-CVE-scanning) includes a comprehensive set of permissions necessary for managing the CVE scan infrastructure. Below is a list of these permissions, along with a description explaining the purpose of each permission within Azure.
| Permission | Description |
|---|---|
| Microsoft.Resources/subscriptions/resourcegroups/write | Enables creation and editing of resource groups. |
| Microsoft.Network/virtualNetworks/write | Enables the creation of virtual networks, fundamental for defining network topologies and settings within Azure. |
| Microsoft.Network/virtualNetworks/subnets/write | Allows creating subnets within virtual networks, crucial for organizing and securing network segments based on different requirements. |
| Microsoft.Network/networkInterfaces/write | Permits the creation of network interfaces, essential for managing how VMs can create internet connections |
| Microsoft.Network/virtualNetworks/subnets/join/action | Allows resources to join subnets, crucial for setting up network configurations for compute resources. |
| Microsoft.Compute/virtualMachineScaleSets/write | Enables the creation of virtual machine scale sets |
| Microsoft.Authorization/roleAssignments/write | Allows assigning roles to users, groups, and services, essential for managing access permissions and ensuring security and compliance across Azure resources. |
| Microsoft.Compute/snapshots/write | Permits creating disk snapshots. |
| Microsoft.Compute/virtualMachineScaleSets/virtualMachines/delete | Deletes a specific Virtual Machine in a VM Scale Set. |
| Microsoft.Storage/storageAccounts/listKeys/action | Allows listing the access keys of storage accounts, enabling operations that require authentication within those storage accounts. |
| Microsoft.Storage/storageAccounts/write | Permits the creation and modification of storage accounts, which are essential for storing snapshots, images, and other data. |
| Microsoft.Compute/galleries/write | Enables creating and managing shared image galleries, useful for managing custom images across the Azure environment. |
| Microsoft.Storage/storageAccounts/blobServices/containers/write | Allows writing to blob service containers in storage accounts, essential for data storage and management. |
| Microsoft.Compute/galleries/images/write | Permits creating and managing images within shared image galleries, facilitating the use of custom images. |
| Microsoft.Compute/images/write | Enables the creation and management of standalone VM images, which can be used to create VM instances. |
| Microsoft.Compute/galleries/images/versions/write | Allows managing versions of images within a shared image gallery, ensuring the use of the correct image versions. |
| Microsoft.Compute/images/delete | Permits the deletion of standalone VM images, allowing for the cleanup and management of unused images. |
| Microsoft.Compute/galleries/images/versions/delete | Enables deleting specific versions of images within a shared image gallery, helping maintain version control. |
| Microsoft.Compute/snapshots/delete | Allows deleting disk snapshots, essential for managing disk storage and ensuring data privacy. |
| Microsoft.Compute/disks/* | Provides comprehensive permissions over disks, including creation, management, and deletion, crucial for VM storage. |
| Microsoft.Compute/disks/beginGetAccess/action | Permits initiating the process to obtain access to a disk, necessary for operations like snapshot creation. |
| Microsoft.Compute/virtualMachineScaleSets/virtualMachines/* | Allows full control over virtual machines within scale sets, including creation, modification, and deletion, essential for scalable deployments. |
| */read | Grants access to read actions for all resource types of all Azure resource providers. |
Updated 12 months ago
